Amazon Instance Connect Endpoint
This blog post will explore Amazon EC2 Instance Connect Endpoint's features, benefits, and how to leverage it for secure remote access to your EC2 instances.
Join the DZone community and get the full member experience.
Join For FreeIn the realm of cloud computing, Amazon Web Services (AWS) EC2 instances have gained immense popularity for their scalability, flexibility, and reliability. Managing these instances often requires remote access for administrative tasks, debugging, or troubleshooting. To address the security concerns associated with traditional bastion hosts and security key management, AWS recently introduced the Amazon EC2 Instance Connect Endpoint Service. In this blog post, we will delve into the details of Amazon EC2 Instance Connect Endpoint, its features, benefits, and how to leverage it for secure remote access to your EC2 instances without associated public IP.
Why Instance Connect Endpoint?
The Amazon EC2 Instance Connect Endpoint is a service provided by AWS that revolutionizes SSH access to EC2 instances. Traditionally, managing SSH access to AWS EC2 servers required solutions like bastion hosts and public IPs to the instances. However, EC2 Instance Connect simplifies this process by leveraging AWS Identity and Access Management (IAM) policies to grant temporary, time-bound access to EC2 instances.
Previously, even with EC2 Instance Connect, having a public IP was still necessary to connect to instances. However, AWS has recently introduced a groundbreaking feature called the Endpoint Service for Instance Connect. With this service, there is no longer a need for public IPs on your instances. Instead, you can securely connect to your instances directly through the AWS console or command line from your local machine.
Key Features and Benefits
- Connect to EC2 instance without public IP. Internet Gateway is not required for your VPC.
- Access control is a combination of Security Group and Identity and Access Management.
- Log all connections in CloudTrail.
How It Works
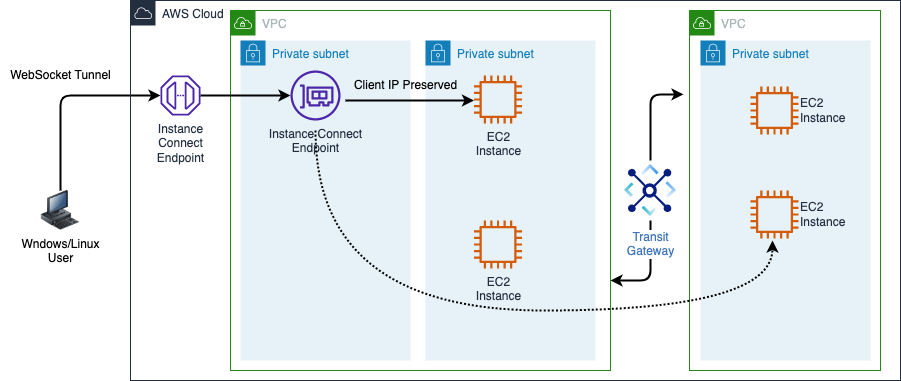
The EIC (EC2 Instance Connect) Endpoint is a TCP proxy incorporating identity awareness. It operates in two modes.
In the first mode, the AWS CLI client is utilized to create a secure WebSocket tunnel from your workstation to the EIC Endpoint using your AWS Identity and Access Management (IAM) credentials. Once the tunnel is established, you can direct your preferred client to your loopback address (127.0.0.1 or localhost) and connect to the desired resources as usual.
In the second mode, when the AWS CLI is not used, the AWS Management Console provides a secure and seamless access experience to resources within your Virtual Private Cloud (VPC). Authentication and authorization processes are evaluated before the traffic reaching the VPC.
EIC Endpoint Configuration
I assume you have enough AWS privileges to configure EC2 Instance connect endpoint.
1. Create an EIC Endpoint
Go to the endpoint option in the VPC service and create a new endpoint.

2. Provide a Permission to Users To Connect EIC Endpoint
Prepare the custom policy according to your IP and Endpoint details and assign it to users who want to connect to EC2 instances.
{
"Version": "2012-10-17",
"Statement": [{
"Sid": "EC2InstanceConnect",
"Action": "ec2-instance-connect:OpenTunnel",
"Effect": "Allow",
"Resource": "arn:aws:ec2:ap-southeast-2:11111111111:instance-connect-endpoint/eice-123456789abcdef",
"Condition": {
"NumericEquals": {
"ec2-instance-connect:remotePort": "22"
},
"IpAddress": {
"ec2-instance-connect:privateIpAddress": "10.0.0.0/16"
},
"NumericLessThanEquals": {
"ec2-instance-connect:maxTunnelDuration": "60"
}
}
},
{
"Sid": "Describe",
"Action": [
"ec2:DescribeInstances",
"ec2:DescribeInstanceConnectEndpoints"
],
"Effect": "Allow",
"Resource": "*"
}
]
}3. Network Access With Security Groups
You have to manage two security groups
- EIC Endpoint Security group:
You only need to configure an outbound rule for the EIC Endpoint security group. It will ensure that EIC Endpoint will be connected to a specific private IP range in AWS.
- Instance Security group:
You must configure EC2 instance security group to allow traffic from EIC Endpoint. The best way is to enable EIC Endpoint security group ID in your Instance security group rule.
Connect EC2 Server from Console
- Open the Amazon EC2 console by navigating here.
- In the navigation pane, click on "Instances" to view your instances.
- Select the instance you want to connect to.
- Click on the "Connect" button, which is located at the top of the console.
- In the connection options, choose "EC2 Instance Connect Endpoint" to utilize the browser-based client.
- A new browser tab or window will open, displaying the EC2 Instance Connect Endpoint interface.
- If prompted, enter the Username, Max Tunnel Duration, and Endpoint.
- Once the connection is established, you can interact with the instance using the browser-based client.
Following these steps, you can connect to an instance using the Amazon EC2 console and leverage EC2 Instance Connect for a seamless and secure connection experience.

Connect EC2 Server from CLI
Enabling connections to an instance involves using the open-tunnel command from the AWS CLI to start a listening mode for new TCP connections. Then, you can utilize SSH to establish additional TCP connections and create private tunnels to your instance. Here's how you can proceed:
Create a tunnel:
aws ec2-instance-connect open-tunnel --instance-id i-094ce4206fa296979 --local-port 8888
Open another terminal and connect to the Instance with your private key:
ssh -i eic-key.pem ec2-user@localhost -p 8888
To connect to a Windows instance without a public IPv4 address or public DNS name, you can utilize Remote Desktop Protocol (RDP) over EC2 Instance Connect Endpoint. This feature allows you to establish an RDP connection to the instance securely. Here's how you can proceed:
Create a tunnel:
aws ec2-instance-connect open-tunnel --instance-id i-00518ad1164dfd6f6 --local-port 3389 --remote-port 3389Use the RDP client to connect Windows server.

Endpoint Limitations
- Connections to an instance using IPv6 addresses are not supported by the EC2 Instance Connect Endpoint.
- For connections where client IP preservation is enabled, the instance being connected to must be located in the same Virtual Private Cloud (VPC) as the EC2 Instance Connect Endpoint.
- It's important to note that client IP preservation is not supported when traffic is routed through an AWS Transit Gateway.
- Please be aware that certain instance types do not support client IP preservation. These instance types include C1, CC1, CC2, CG1, CG2, CR1, G1, G2, HI1, HS1, M1, M2, M3, and T1.
Conclusion
AWS provides various methods to connect to instances, including SSH, RDP, AWS Systems Manager Session Manager, EC2 Instance Connect and Endpoint, bastion hosts, and VPN. The choice of method depends on the operating system, security requirements, network configuration, and personal preference. By leveraging these connection methods, you can securely access and manage your AWS instances based on your specific use cases and requirements.
Opinions expressed by DZone contributors are their own.

Comments