Architecting a Completely Private VPC Network and Automating the Deployment
Learn how to design and build a truly private virtual private cloud (VPC) network architecture and deploy the architecture with Terraform automation.
Join the DZone community and get the full member experience.
Join For FreeIn today's cloud world, security has taken precedence over resiliency and high availability. With the introduction of Virtual Private Cloud, network security has become critical. In this article, you will learn the best practices to make a virtual private cloud more private and secure than ever before.
By the end of this article, you will learn how to:
- Design a secured VPC private network
- Best practices in architecting a VPC private network
- Build a high availability VPN and bastion hosts
- Use of Terraform automation for cloud infrastructure provisioning
What Is a Private VPC Network?
A virtual private cloud is completely private if there is no public ingress or outgress network traffic. In simple technical terms, there are no public gateways on the subnets (private subnets) and no floating IPs on the Virtual Server Instances (VSIs).
How Do I Connect to This Private VPC Network?
Client-to-site VPN for VPC is one of the two VPN options available on IBM Cloud that provides a client-to-site VPN solution that allows users to connect to IBM Cloud resources through secure, encrypted connections.
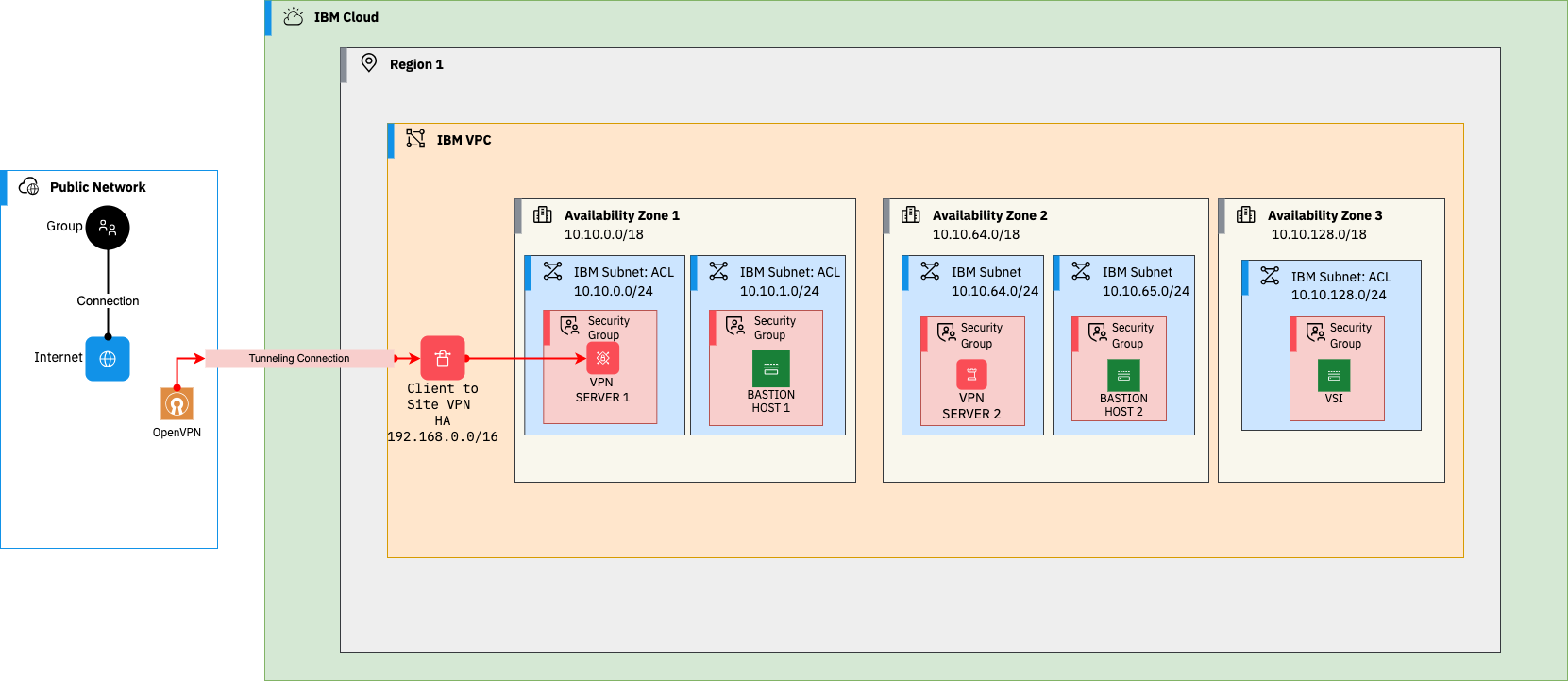
Private VPC architecture
What Does This Architecture Address?
- The bastion hosts and the client-to-site VPN servers are highly available.
- The VPN creates a secure tunnel to connect from a local machine to the Cloud.
- The bastion host accepts SSH connections from client to site VPN (192.168.x.x).
- The last (final) rule in the stateless access control lists is denying all the inbound and outbound traffic.
- No public gateways are attached to the subnets, and no floating IPs on the virtual server instances (VSIs).
- The security groups attached to the VSIs allow traffic only on specific required ports and private IPs.
Prerequisites
- IBM Cloud API Key
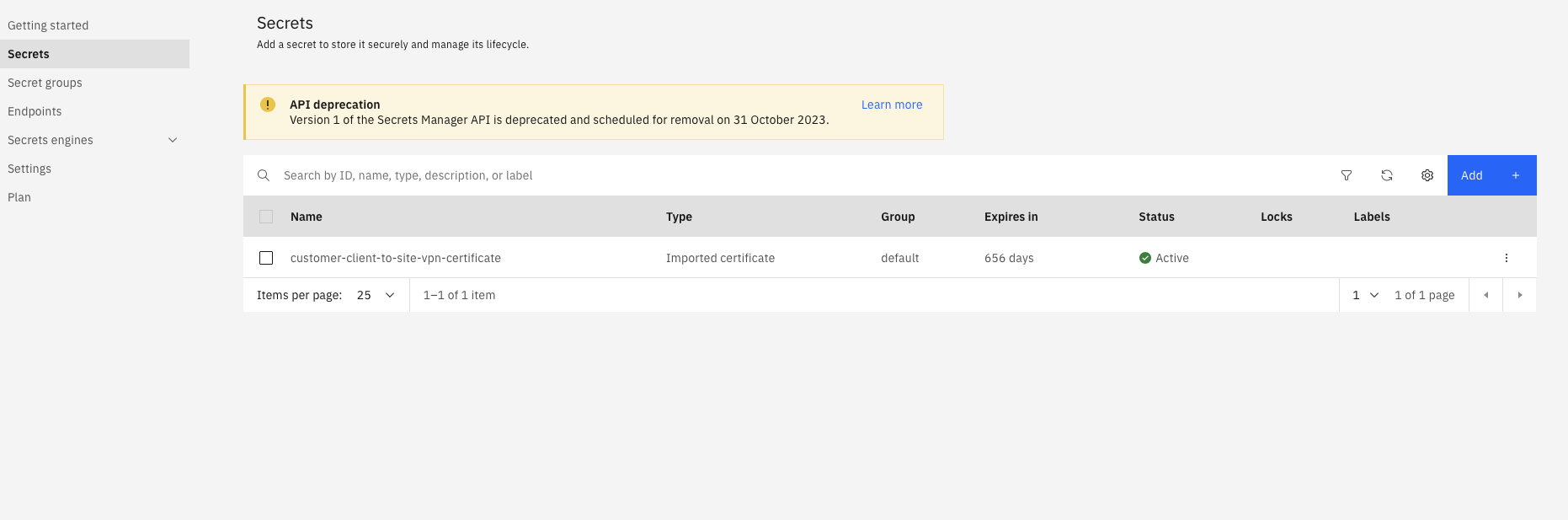
- Certificate's CRN from Secrets Manager
- OpenVPN client to connect to client-to-site VPN from your local machine
- Setup Terraform
Provision of the Private VPC Network Using Terraform
Once you have the secrets manager secret with the certificate, launch your terminal and set the following Terraform variables.
export TF_VAR_ibmcloud_api_key=<IBM_CLOUD_API_KEY>
export TF_VAR_secrets_manager_certificate_crn=<SECRET_CRN>Clone the GitHub repository with Terraform and Ansible code:
git clone https://github.com/VidyasagarMSC/private-vpc-network
cd terraformRun the Terraform commands to provision the VPC resources: subnets, bastion hosts (VSIs), VPN, etc.,
terraform init
terraform plan
terraform applyConnect to Client-To-Site VPN
- Once the VPC resources are successfully provisioned, you need to download the VPN client profile.
- Click the client to site tab and then on the name of the VPN
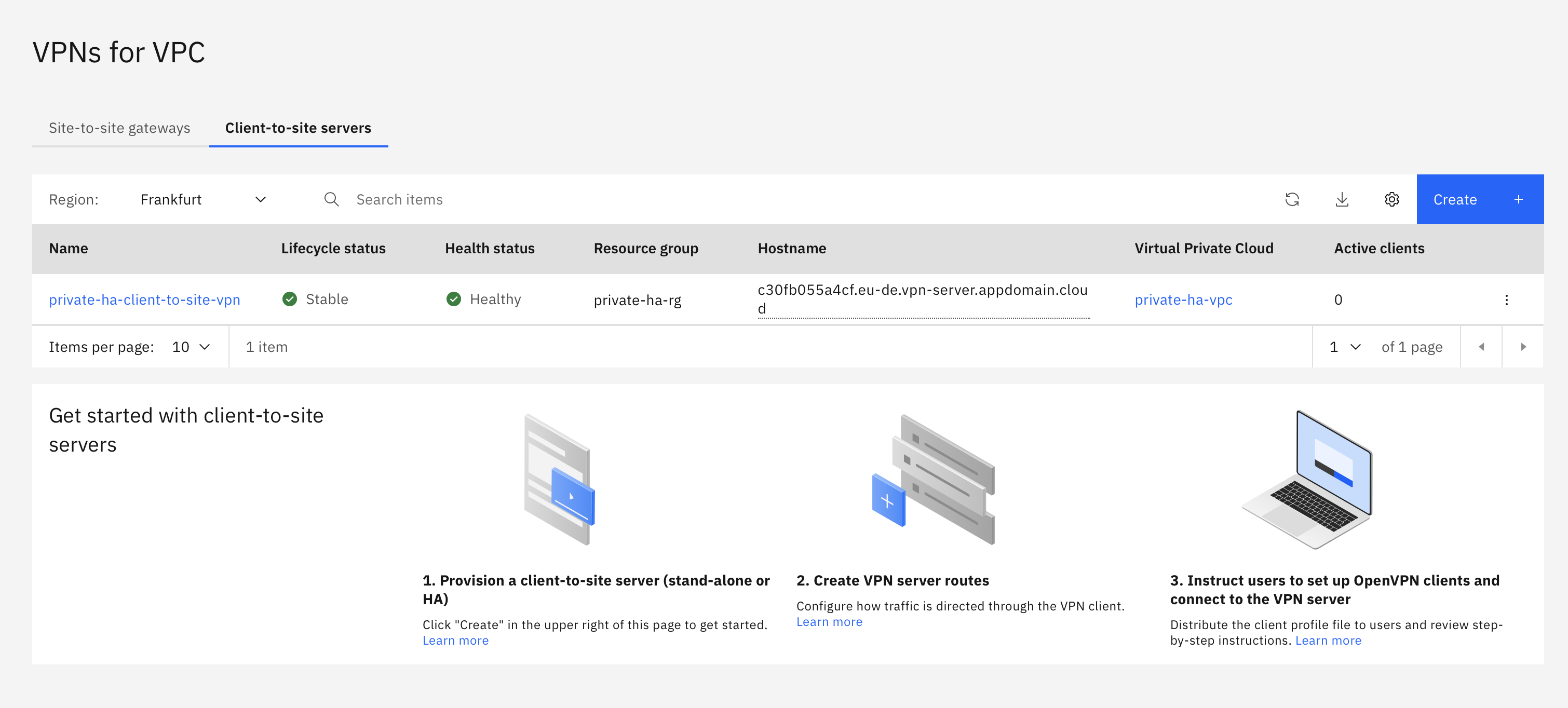
- Download the profile from the Clients tab
- The VPN provisioned through Terraform uses certificates. Follow the instructions here to connect to the ovpn client.
- You should see the successful connection on your OVPN client.

Verify the SSH Connection
On a terminal, add an SSH private key to the SSH agent with the following command
ssh-add <LOCATION_OF_PRIVATE_SSH_KEY>Example: ssh-add ~/.ssh/<NAME_OF_THE_PRIVATE_KEY>
Run the following command to SSH into the RHEL VSI through a bastion host. You will be using the private IP address of the bastion in Zone 1
ssh -J root@10.10.0.13 root@10.10.128.13Command to connect from a bastion host in Zone 2 is ssh -J root@10.10.65.13 root@10.10.128.13
- Remember, you should be connected to the client-to-site VPN to SSH into the RHEL VSI through the bastion host.
- Try disconnecting the VPN and SSHing into the RHEL VSI.
What's Next
- Go through the deployed VPC network architecture and check the ACL and security group inbound and outbound rules.
- Check the client-to-site VPN routes (deliver and translate).
- Though the architecture shows one VPC, this can be expanded to have multiple VPCs, with each VPC playing a different role to bring in the separation of traffic like edge, management, and workload VPCs, respectively.
Opinions expressed by DZone contributors are their own.

Comments